How to develop and manage a robust cybersecurity strategy? Many security officers and managers face this question in turbulent times when they see that the world around them has changed. I had a challenge when I tried to find a single organized and practical framework that answers this question in end-to-end fashion.
Most security frameworks focus on implementing security management systems, but they are too tactical for a strategic program. Some approaches help to understand the overall strategy implementation process, but they lack sufficient details that would allow CISOs to turn the theory into practice. Some useful strategic frameworks focus on IT, but they do not cover information security or cybersecurity issues.
As a result, to develop a successful cybersecurity strategy, you either need a broad experience or you need to merge multiple frameworks available on the market, pick the most critical parts from each of them, put them in the right order and the context of your business. But who has the time for that these days?
To ease your pain, I described an organized and comprehensive approach to Cybersecurity Strategy Management. It mixes techniques inspired by best practices found in IT and information security frameworks, project management, and change management with experience of what works and what does not work in reality.
The approach is heavily impacted by 18 years of my professional experience in information security management and assessing or designing cybersecurity strategies for 14 companies.
My idea is to build a golden source of information for CISOs, security managers, and architects in Cybersecurity Strategy Management.
Structure
Description of all Cybersecurity Strategy Management phases contains the following elements:
Customer Profile
Activities
Organized list of actions to be completed during each of the phases.
Objectives
Key objectives to be achieved - why specific phases is important.
Inputs
Information needed to complete activities during a specific phase.
Outputs
Work products delivered as a result of completed actions.
Practices
Tools, methods, and accelerators that speed up proposed activities.
References
References to market frameworks and standards.
Important Notes
Practices
The following approach to Cybersecurity Strategy Management includes references to market best practices, standards, and frameworks in the area of technology and security. However, it does not follow them to the point. It blends techniques from these frameworks with practices from business strategy development, project management, time management, and change management, including agile and lean methodologies. The most relevant practices are selected based on a professional judgment. Therefore, it cannot be treated as a guarantee of compliance with any of these standards.
Updates
This article is a living article - it is continuously updated. It provides a high-level summary of each strategy management phase, its purpose, actions to complete, required inputs, references to frameworks available in the market, and the results you should produce. In the following weeks, I will focus on describing all 40 activities related to strategy development, implementation, and improvement. As a result, some of the items may change over time.
Cybersecurity Strategy Management
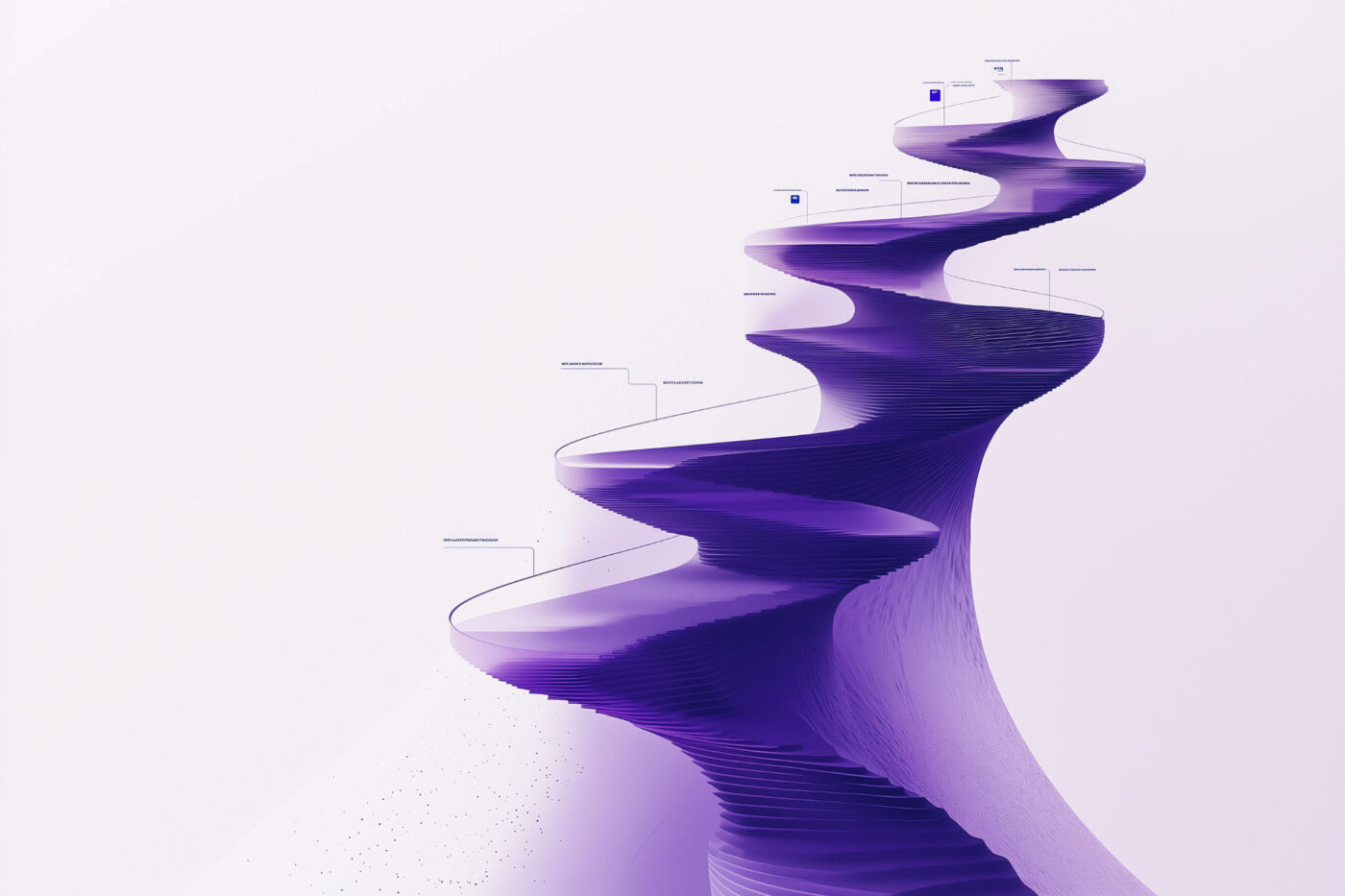
Cybersecurity Strategy Management Lifecycle
1 Horizon
Key objectives to be achieved - why specific phases is important.
2 Destination
Work products delivered as a result of completed actions.
3 Orientation
Tools, methods, and accelerators that speed up proposed activities.
4 Planning
References to market frameworks and standards.
5 Action
Work products delivered as a result of completed actions.
6 Tracking
Tools, methods, and accelerators that speed up proposed activities.
7 Correction
References to market frameworks and standards.
1. Horizon
Understand your territory
Before starting your journey towards a successful cybersecurity strategy, look at your cybersecurity Horizon. Before starting a new trip, a look at the horizon gives us many details about how the terrain looks, how much time we have, the weather, and the obstacles on the road.
In the cybersecurity world, the Horizon phase concentrates on a high-level overview of security change drivers. They include company environment and strategy, technology landscape and IT objectives, technology trends shaping the industry, and regulatory demands. This phase also consists of a threat landscape evaluation to identify critical assets that require protection and the risks your strategy should mitigate.

2. Destination
Define your target location
You cannot plan your journey if you do not know where to go. The vision of your Destination urges you to move. A powerful and convincing image of the future is a critical ingredient of a security strategy. It clearly shows where you want to be and is the baseline for determining your security mission.
To enhance this vision, select the security framework aligned with your Horizon. Prioritize security domains within the chosen framework. You cannot maintain them at the same level because organizational resources are usually limited. Ensure that your energy focuses on the most significant areas.
All the activities at the Destination stage should guide you to a complete target state model. It should describe agreed maturity levels for each security domain and contain a list of required components.
The traditional approaches to security strategy usually recommend defining the Destination after analyzing the current state. However, I advise switching the order of these phases. It helps ensure that you are not stuck in the presence or past and take a refreshed approach to paint the future vision. It is also more logical for me – you need a reference model ready before you can identify potential gaps.

3. Orientation
Understand where you are now
Knowing the destination is not sufficient to plan the journey. You need a starting point to pick the best route and assess alternate ways of getting to your destination. The same approach applies to security strategy. The strategy needs an action plan to be effectively implemented. To develop a supporting roadmap, you need both reference points – your starting location and destination.
The purpose of Orientation is to help you find your current location.
At this stage, review your current state. Analyze where is the security function in terms of processes maturity, skills, and technology. Complete this analysis using your target state model supported by relevant statements from the selected security framework. Identify discrepancies between your current state and your Destination, existing issues, strengths upon which to build, and cost-saving opportunities.
The key output from the Orientation phase is a set of prioritized recommendations. They should outline what you need to do to reach your Destination.

4. Planning
Plan how to reach your target
It is easy to organize a one-day trip.
It takes more to arrange an annual expedition.
The process of Planning comes into play here. It helps translate multiple actions into manageable projects, workstreams, and achievable objectives that can be tracked and controlled using a high-level plan.
During the Planning phase, aggregate all recommendations into manageable projects. Describe these projects with necessary details, including their ownership, deliverables, resources, and milestones. They will help you evaluate each project’s complexity, agree on its priority, and place associated goals on the roadmap. When the roadmap is ready, document your strategy, ask your stakeholders to review it, incorporate feedback, and organize its formal approval.
Communicate the final version of the strategy to all relevant stakeholders. As long as you engaged them in all previous stages, it should be no surprise for them. Its buy-in and successful implementation depend on it.

5. Action
Achieve your strategic objectives
The Action phase usually drains most of your time and resources.
It aims to turn your strategic vision into reality.
To implement the strategy, translate your high-level roadmap into specific operational plans. Since the implementation success depends on the people, their behaviors, and organizational culture, define a change management approach that considers human factors.
At this stage, project managers responsible for the respective workstreams will start working on defined activities. They will establish new organizational structures, document required policies, establish or change security processes, implement required technology solutions, build user awareness and implement reporting to track progress against agreed objectives.
Execution of all agreed plans should increase the maturity of your security capabilities to the levels you determined as your desired target state. As a result, the risks recognized during your Horizon phase should be minimized to an acceptable level.
6. Tracking
Track current location and progress
To guarantee that you are heading in the right direction, you need to continually track your current location. The purpose of the Tracking phase is to help you stop for a while, have a look at your map, see if you can still recognize your surroundings and which turn to take next.
During the Tracking phase, focus on two types of activities. Measure your progress against objectives and report achieved business benefits to relevant stakeholders to ensure their continuous dedication and ongoing support. Their feedback can help you identify what is not working as intended and make revisions to your strategy or implementation roadmap.
At the same time, try to be conscious of any changes in the business factors that impact security. Parts of your strategy can change based on current business conditions.
The Tracking phase’s objective is to ensure that you are still heading in the right direction and do not follow the previous path blindly if the terrain topography has changed.

7. Correction
Correct your path to omit obstacles
Cybersecurity strategy is not set in stone. Even if your journey’s target is the same, the trail you choose may change based on obstacles you encounter on the road and alternate, better routes you can take. You may need a Correction to your course.
At this stage, based on your successes, lessons learned from your actions, and expected changes, you can identify potential improvements. Estimate their complexity. Their implementation may involve making small adjustments to your strategic vision, capability models, or strategic roadmap.
However, sometimes you may notice a severe misalignment of the current strategy with your Horizon. In this scenario, minor improvements may not be sufficient, and it may be more beneficial to restart the cycle by going into the Horizon phase. This decision is the call that you can make based on your judgment.